Deconstructing the Octopus
On 2 Jan, 2014 By Marilyn 0 Comments


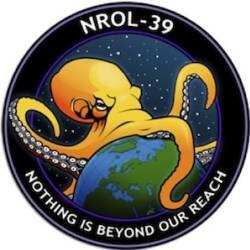
A colleague of mine, Michael Walker, from the newly formed Data Science Association, sent me an email with an outrageous logo.
Yes, this is the logo for a satellite launched by the United States on December 5, 2013, even with the backdrop of Snowden’s NSA revelations.
Michael describes the “pure chutzpah arrogance” of the The National Reconnaissance Office (NRO). So here we have it: The NSA mooning its people, spreading its tentacles into my house, my bedroom, yes anywhere it wants to go. This creature is almost childlike, yet reminiscent of Medusa, the “guardian protectress” who turned her onlookers to stone.
As I studied the creature my mind wandered back in time to my birthplace, Albuquerque, New Mexico. My parent’s humble, tiny, stucco house was within a few miles of the site where Bill Gates founded Microsoft Corporation in 1975. My father was an electrical engineer at Sandia Laboratories, an adjunct lab to the infamous Los Alamos. Born into poverty due to the Great Depression of 1929, he survived that harsh elements of the San Luis Valley in Colorado on $3.81 one winter with his mother and step-father. On his eighteenth birthday he was conscripted into General Patton’s 6th Armored Division and like so many of his comrades saw the worst of the worst, the unthinkable. These men marched through Italy, France and Germany. Yes, they saw the unspeakable: Buchenwald concentration camp.
Never again, never again. These men returned home and pounded the table every night at the dinner table. Never again in the history of man can such evil be upon man. There were two messages: 1. Keep a strong defense and 2. Never let the middle class fall. With that the United States opened up the purse strings and pursued technology as the answer to all evil.
Within forty years, from the early 1950’s through the mid 1990‘s the world was revolutionized. Silicon based devices would run the world: the stock exchange, the electrical grid and air traffic control. Vacuum tubes were replaced by transistors, then semiconductors. Fast running processors would herald in the personal computer.
Graphical user interfaces and browsers would help connect computers around the world via a standard protocol and the internet was born. Databases would remember bank accounts, transactions and phone conversations. Copper wire connecting home telephones would be replaced by TCP/IP, clients and servers exchanging information and data transfer so fast the human cannot comprehend or manage it.
In 1976 something interesting happened. Two American cryptographers, Whitfield Diffie and Martin Hellman published a method for two computers to exchange encrypted messages. Known as as the Diffie-Hellman key exchange, two computers on a network could generate keys that only they agreed upon and exchange secret messages. This was the envy of every intelligence officer on earth. Without the keys, eaves dropping was not possible. This poised a problem for our intelligence community. In the day of copper wire, a requesting agency simply obtained a court order, installed a listening device and eaves dropped. The scope was limited, targeted and the American people agreed to this invasion.
Diffie-Hellman on the other hand, locked the spies out. The agencies were so concerned that they proposed a Clipper chip be installed in every computing device, including today’s mobile phone devices. This would allow an intelligence agency to break encryption on any computing device. By 1996 the government gave up on the Clipper set and apparently reverted to other schemes, such as collecting meta data about every single phone call made in the United States. The agencies also wanted to hold a decryption key in escrow, just in case they ever needed to break into communications. Recent revelations by Snowden indicate that the intelligence agencies may have weakened encryption algorithms in their own favor and have effective backdoors into computing devices. These privacy issues remain today, even as we speak.
Spying is dirty business. Ask AlanTuring. Turing effectively broke Hitler’s back by applying probabilistic models to German communications and broke German encryption. He is also the father of modern day computer science, the daddy of algorithms. When asked what can I compute and what is not computable, mathematicians turn to the Turing machine. The Turing machine is the formal mathematical model that effectively proves questions such as, “Can we translate one human language to another?” The answer is indeed, no. That aside, Alan Turing was a homosexual and homosexuality was not legal in 1952. He was criminally prosecuted, forced to take female hormones and died of cyanide poisoning.
We all remember 9/11, the images of planes flying into the World Trade Center. How could that be? How did the intelligence community miss this one? No one flies planes into buildings on our soil and no one explodes pressure cookers at the Boston marathon. Yet it happened and Americans have had enough. They demand their intelligence community predict all bad actors, yet want the privacy of their bedroom.
The little octopus, like chutzpah, can be good or it can be bad. Provoked the creature can morph into a multi-headed, snake infested creature turning its onlookers into stone. Like Medusa it is a warning to my enemies and like a child it learns and grows.
Casually, the animal is known for its innocence, its intelligence and ability to learn. Its tentacles reach for food and sensation. The little octopus may not be so stupid after all.
Has intelligence gone too far? Yes, I think so. But we must behave as a nation of realists and learn to balance our need for privacy and security as adults, in a court of law, not as all knowing individuals that believe we have infinite wisdom about what is good and what is evil.
